Windows Subsystem for Linux (WSL)

WSL is a Windows feature that allows you to run a complete Linux environment, including command-line tools and applications, directly on your Windows machine without a virtual machine or dual-boot setup. WSL 1 uses a translation layer for compatibility, WSL 2 makes use of virtualization. Seems cool for attackers to use, Lolbin, Linux, potential logging evasion through virtualization, application bypass..
Exploring WSL:
Install from a pre-set list of distributions.

Upon install we see the following execution flow. We also see the child wslhost.exe of the initial distro install command, within that argument is a distro ID which is displayed every time a wsl session is started.
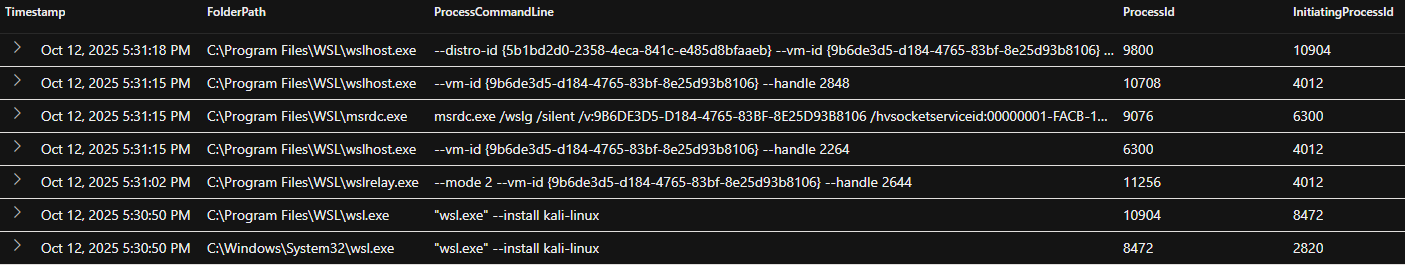
You can reg query this GUID against the host to reveal the distro name. This GUID will be bespoke to that device.

A ShellLinkCreateFileEvent will generate off the back of an LNK creation from the install by the parent of Windows Subsystem for Linux Service. This will indicate the distro installed.

Now let’s test both command and execution within the session to evaluate the telemetry in Defender.
Testing the below Linux commands provided zero evidence in process events. But as expected, network events are still present however there is no indication of process name or PID.
whoami curl -s "https://api.ipify.org?format=json" wget -qO- https://api/ipify.org
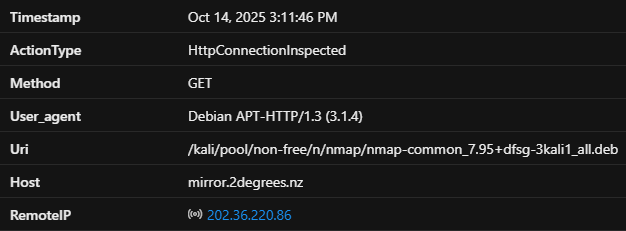
For execution I tested nmap. Again, zero indication of process or file telemetry. However we can identify the initial pull from apt-install using the displayed user agent ‘Debian APT-HTTP’. This is a useful indicator and can provide insight into package requests. This will also be visible in any proxy logging.
sudo apt install nmap nmap -sS --top-ports 100 -T4 -sV scanme.nmap.org
WSL is cross directional, Windows commands and binaries can still be executed within the WSL session.
For example running Calc.exe from within the WSL will provide process logging.
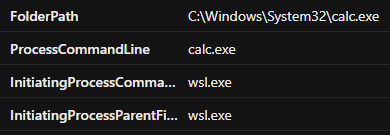
Executing cmd.exe /c "net localgroup Administrators" does the same. Execution shown under wsl.exe.

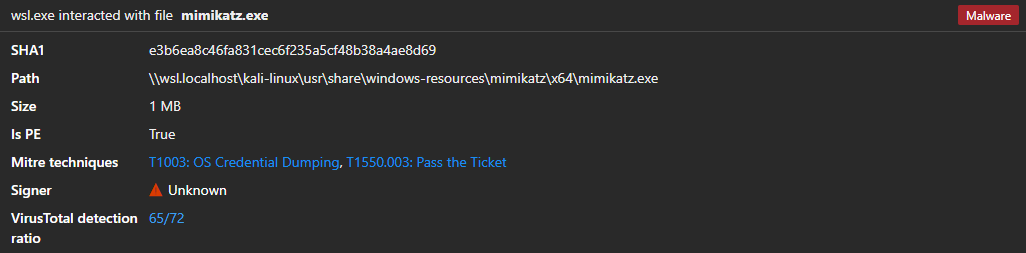
Files part of the subsystem are stored in \\wsl.localhost\(distroName)\*. There is zero logging regarding this path including file or process events from Defenders perspective. The only visibility is within the alert story from a detection.
To provide insight into WSL events, install the WSL plugin.
https://learn.microsoft.com/en-us/defender-endpoint/mde-plugin-wsl