EDR Freeze

https://github.com/TwoSevenOneT/EDR-Freeze
EDR-Freeze is a PoC that suspends EDR/AV processes from user mode by abusing Windows Error Reporting’s WerFaultSecure.exe. It calls the MiniDumpWriteDump function in DbgHelp to start a process dump, this operation suspends the target to capture a snapshot. If WerFaultSecure.exe itself is suspended while the dump is in progress, the target process remains frozen indefinitely.
To do this against a PPL (Protected Process Light) process such as MsMpEng, the leveraged process must be of PPL level or higher. WerFaultSecure typically runs at WinTCB, the highest.
Attack Path
1. Launch WerFaultSecure as PPL.
2. Start a dump of the target process, MsMpEng.exe.
3. While WerFaultSecure.exe suspends MsMpEng.exe, suspend WerFaultSecure.exe itself.
4. Target process MsMpEng.exe remains frozen.
No BYOVD driver is needed; this avoids kernel-driver bypasses and signing hurdles and is easily accessible as WerFaultSecure is always present on the operating system. A Lolbin.
Now this was posted on Git 21/9/25 and here is me running this Sept 28/9/25. I were unable to freeze MsMpEng or MsSense as user, admin or system. However, we could freeze less privileged processes such as Calculator.exe. I may have been late to the party and this was already patched. Even so, attempts of this attack are still valuable from a hunting perspective and a learning exercise.
So lets run this. Here we supply the target PID and the freeze time in milliseconds.
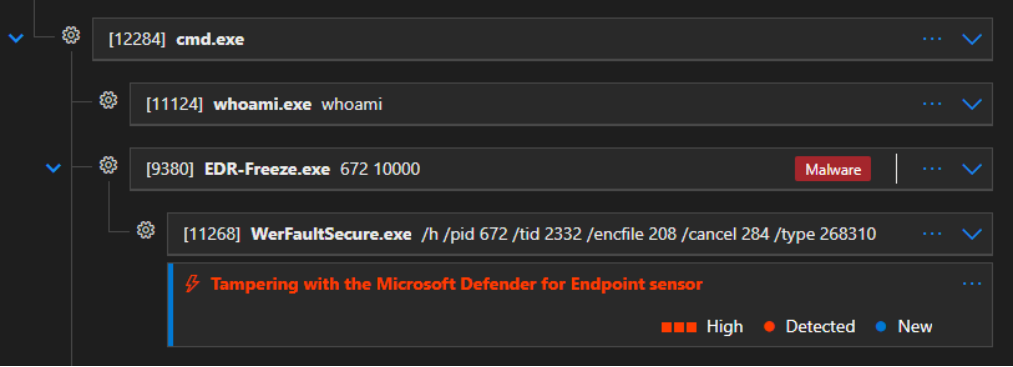
Here is the execution flow in Defender.

Thread state.

WerFaultSecure.exe runs under SYSTEM in normal operation; user context execution is anomalous. It should only be parented by signed Windows processes. A typical invocation is ‘WerFaultSecure.exe -p 10080 -s 3716’ where -p is the process ID of the crashed process. In the context of EDR Freeze. We observe unique flags that be used for detection which are super valuable for sus activity.
/h: Triggers secure dump mode hidden function
/pid: Process ID to dump
/tid: Main thread of the process to dump
/encfile: Encrypted crash dump file
/cancel: Cancel event
/type: MIMDUMPTYPE flags
So we can now come up with a query. WerFaultSecure executed under a user context where MIMDUMPTYPE flags are present from an unsigned parent. Extract the target PID within the commandline execution of WerFaultSecure and correlate onto matching PIDs relating to MsMpEng.
let SusWerFaultPIDs =
DeviceProcessEvents
| where FileName =~ "WerFaultSecure.exe" and ProcessCommandLine has "/type"
| where InitiatingProcessSignatureStatus != "Valid" or InitiatingProcessAccountDomain != "nt authority"
| extend WerFaultTargetPID = toint(extract(@"(?i)(?:^|\s)(?:-p|/pid|pid)\b\s*=?\s*(\d+)", 1, ProcessCommandLine))
| where isnotempty(WerFaultTargetPID)
| project
WerFaultSecureTime=Timestamp,
WerFaultTargetPID,
WerFaultSecureCommandLine=ProcessCommandLine,
WerFaultSecureInitiatingProcessCommandLine=InitiatingProcessCommandLine,
WerFaultSecureInitiatingProcessFolderPath=InitiatingProcessFolderPath,
WerFaultSecureInitiatingProcessSignatureStatus=InitiatingProcessSignatureStatus,
DeviceName;
// Freezing
DeviceProcessEvents
| where Timestamp >= ago(30d)
//| where FileName in~ ("MsMpEng.exe", "MsSense.exe") ← insert FileName or not
| join kind=inner (SusWerFaultPIDs) on $left.ProcessId == $right.WerFaultTargetPID and DeviceName
| project
TargetTimestamp=Timestamp,
WerFaultSecureTime,
DeviceName,
WerFaultSecureCommandLine,
WerFaultSecureInitiatingProcessCommandLine,
WerFaultSecureInitiatingProcessFolderPath,
WerFaultSecureInitiatingProcessSignatureStatus,
WerFaultTargetPID,
TargetFile=FolderPath,
TargetProcressId=ProcessId
| where WerFaultSecureTime > TargetTimestamp

Simplifying this, query and review any unsigned parent execution of WerFaultSecure from a user context. This would also satisfy other forms of suspicious activity such as process dumps.
DeviceProcessEvents | where FileName =~ "WerFaultSecure.exe" | where InitiatingProcessSignatureStatus != "Valid" or InitiatingProcessAccountDomain != "nt authority" | where isnotempty(InitiatingProcessAccountName) | project TimeGenerated, DeviceName, InitiatingProcessAccountName, FolderPath, ProcessCommandLine, InitiatingProcessCommandLine, InitiatingProcessSignatureStatus
Now from a Defender detection perspective. It did alert against Freeze attempts for MsSense as system tampering. At the time of writing EDR-Freeze did not initially detect as malware when written to disk.